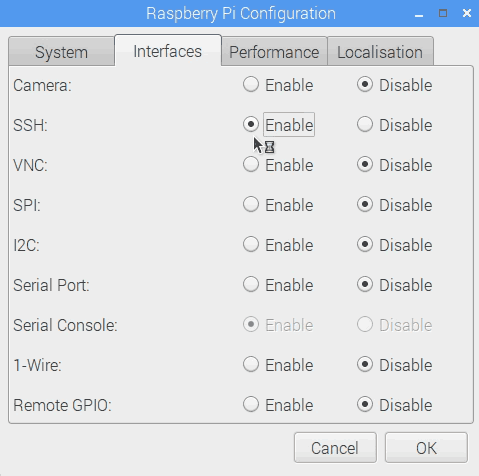
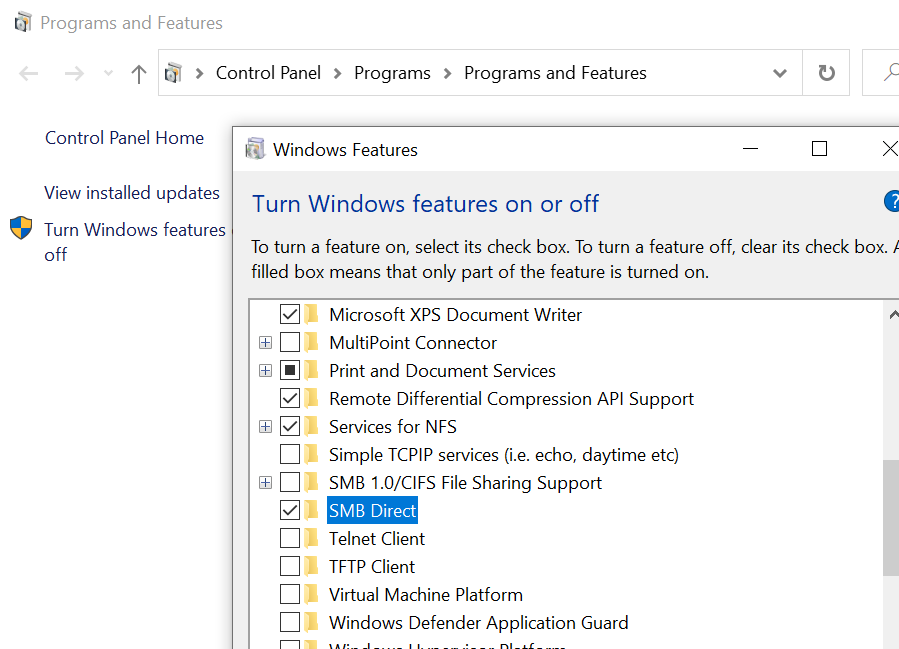
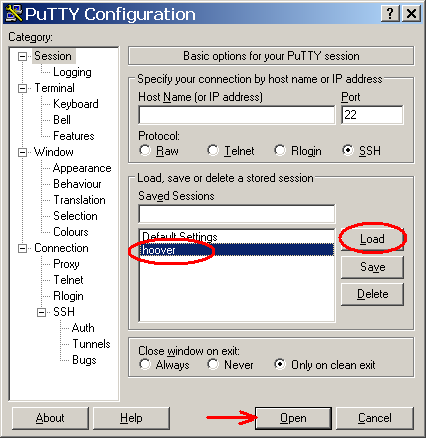
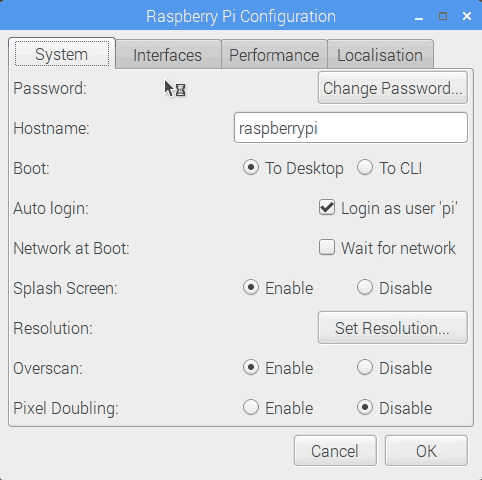
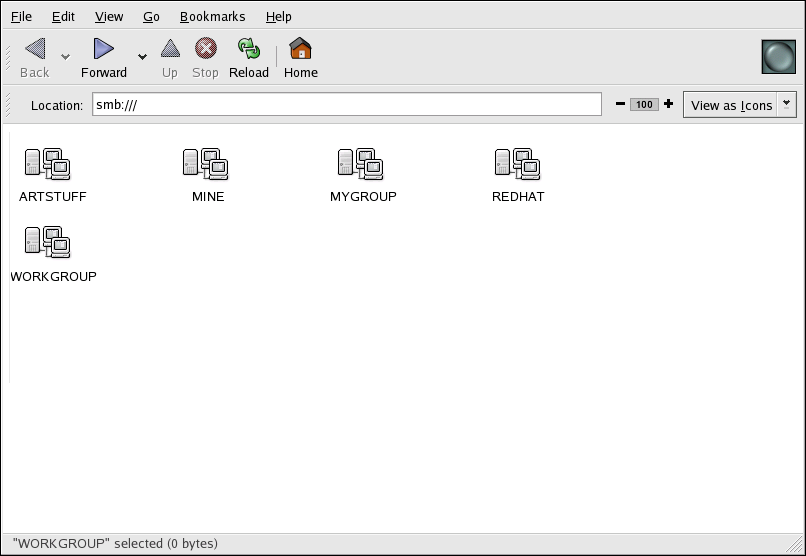
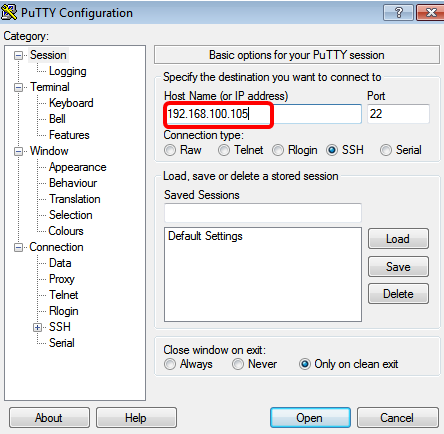
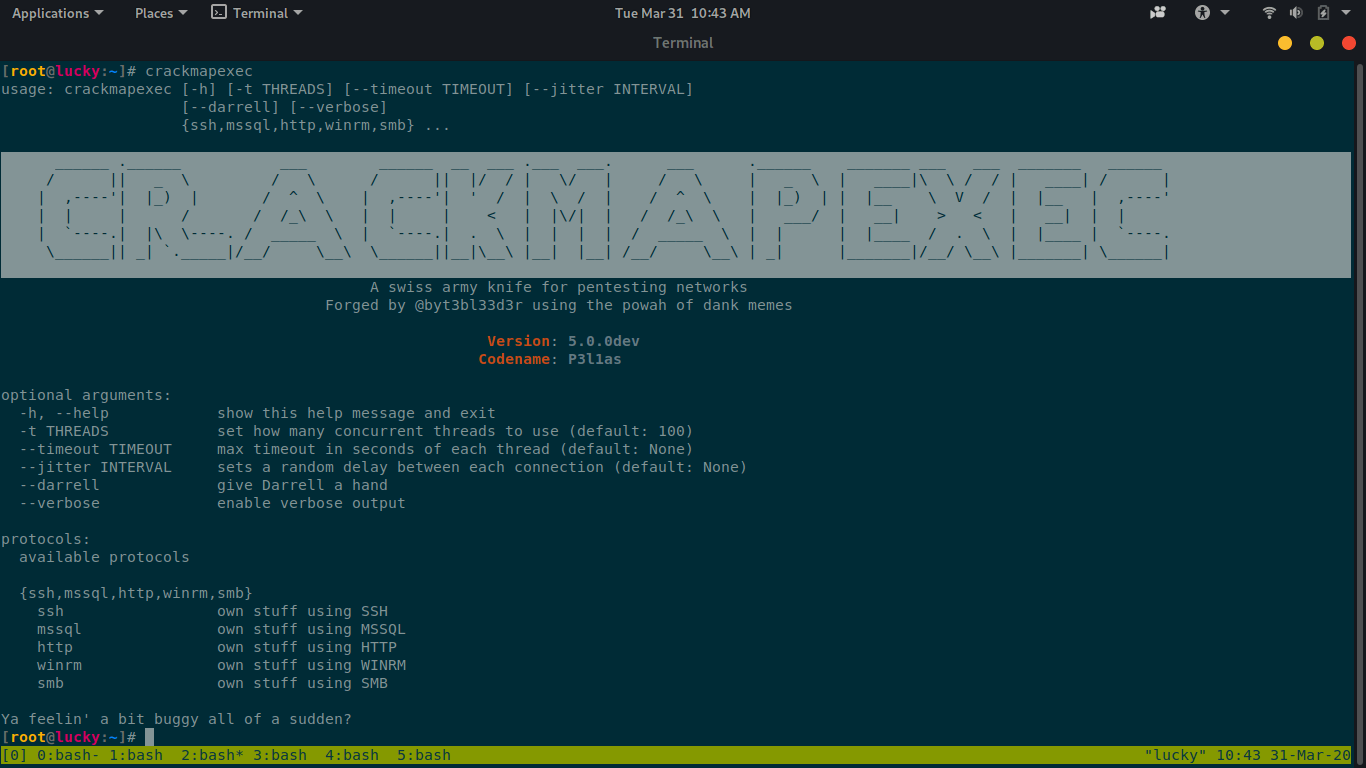
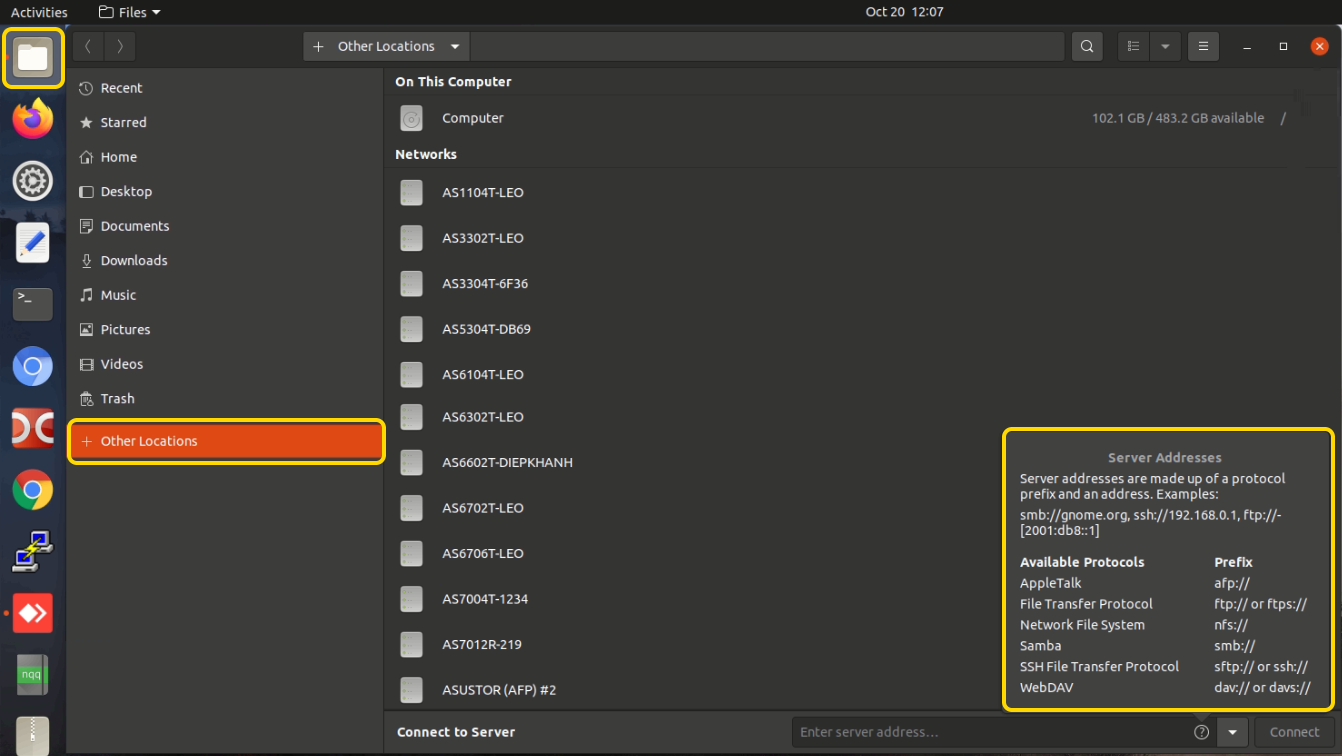
How To Exploit smb and ssh | Port 22, 139, And 445 Exploit | With Try Hack Me Network Services Room - YouTube

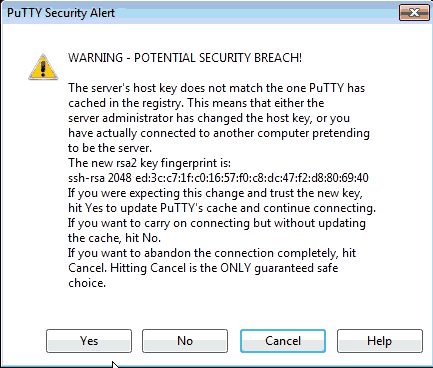
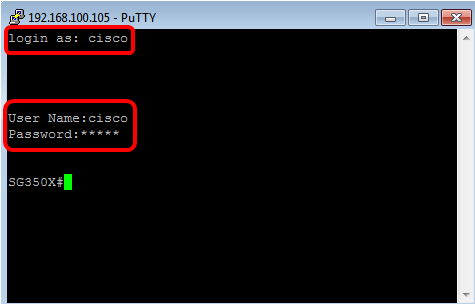
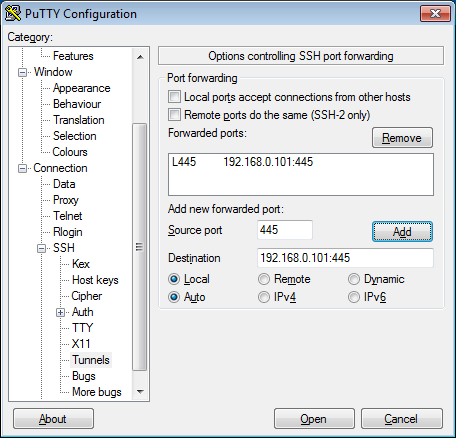
ExtraHop on Twitter: "Secure Shell (#SSH) is a well-designed protocol with good cryptography for securely accessing remote devices. It is also one of the most widely used protocols, making it a favorite