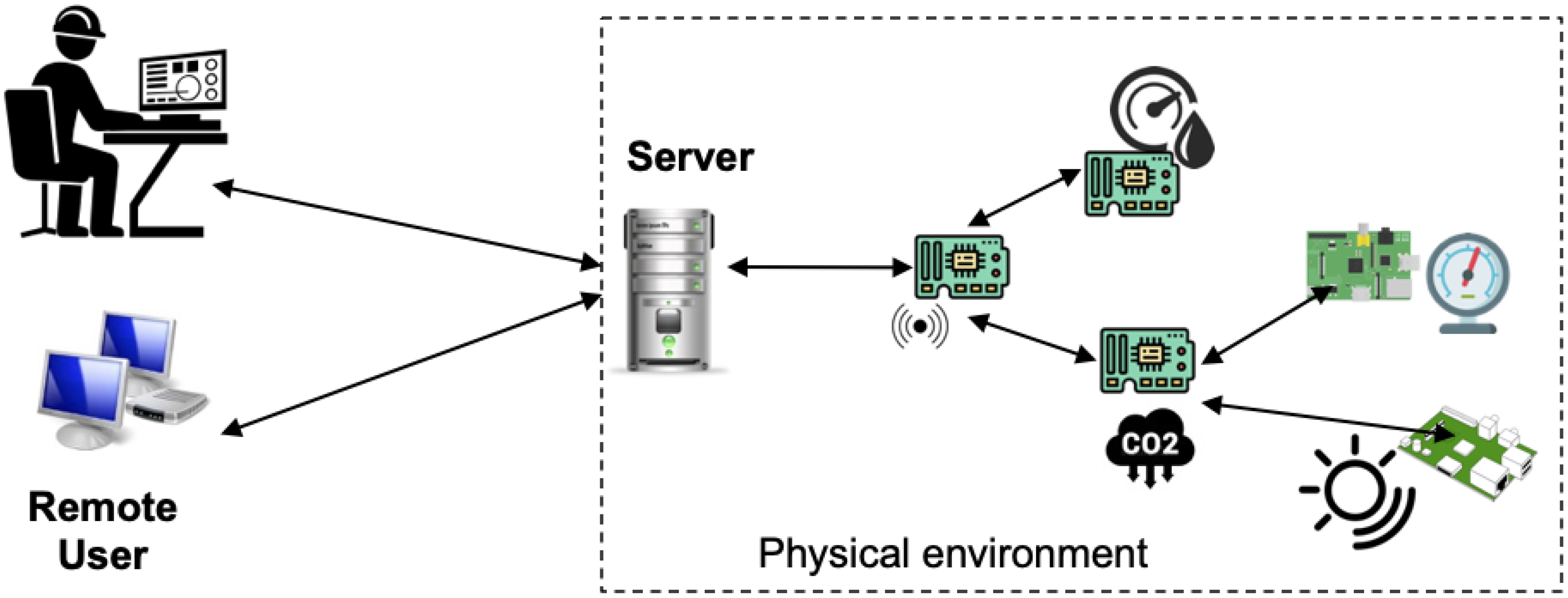
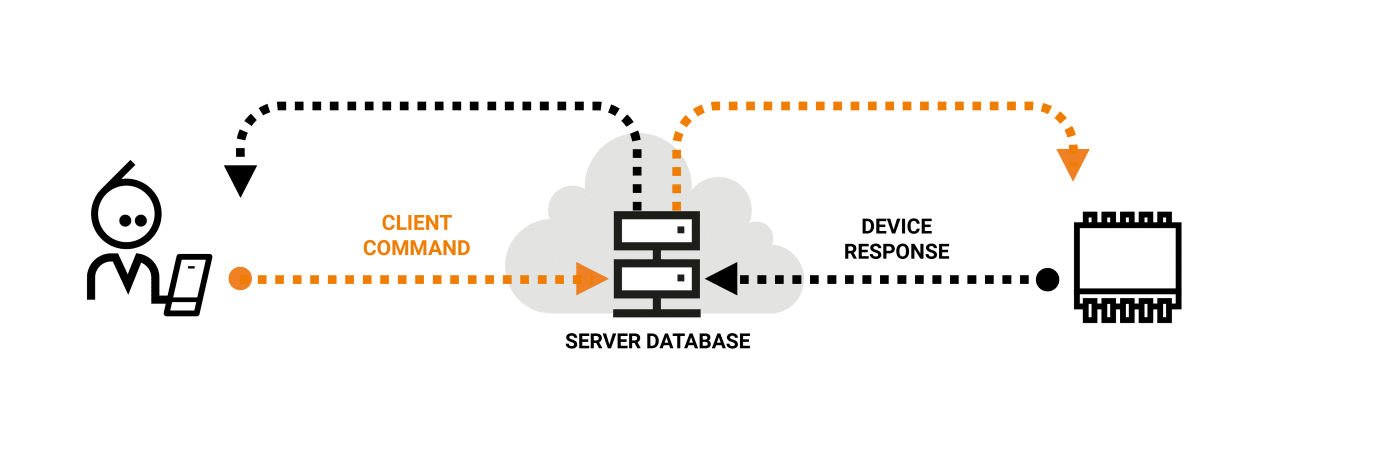
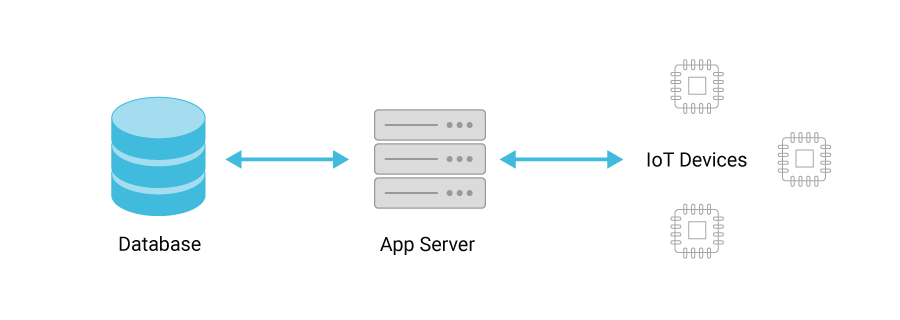
Threat model: an IoT device communicates with a server in the Internet;... | Download Scientific Diagram

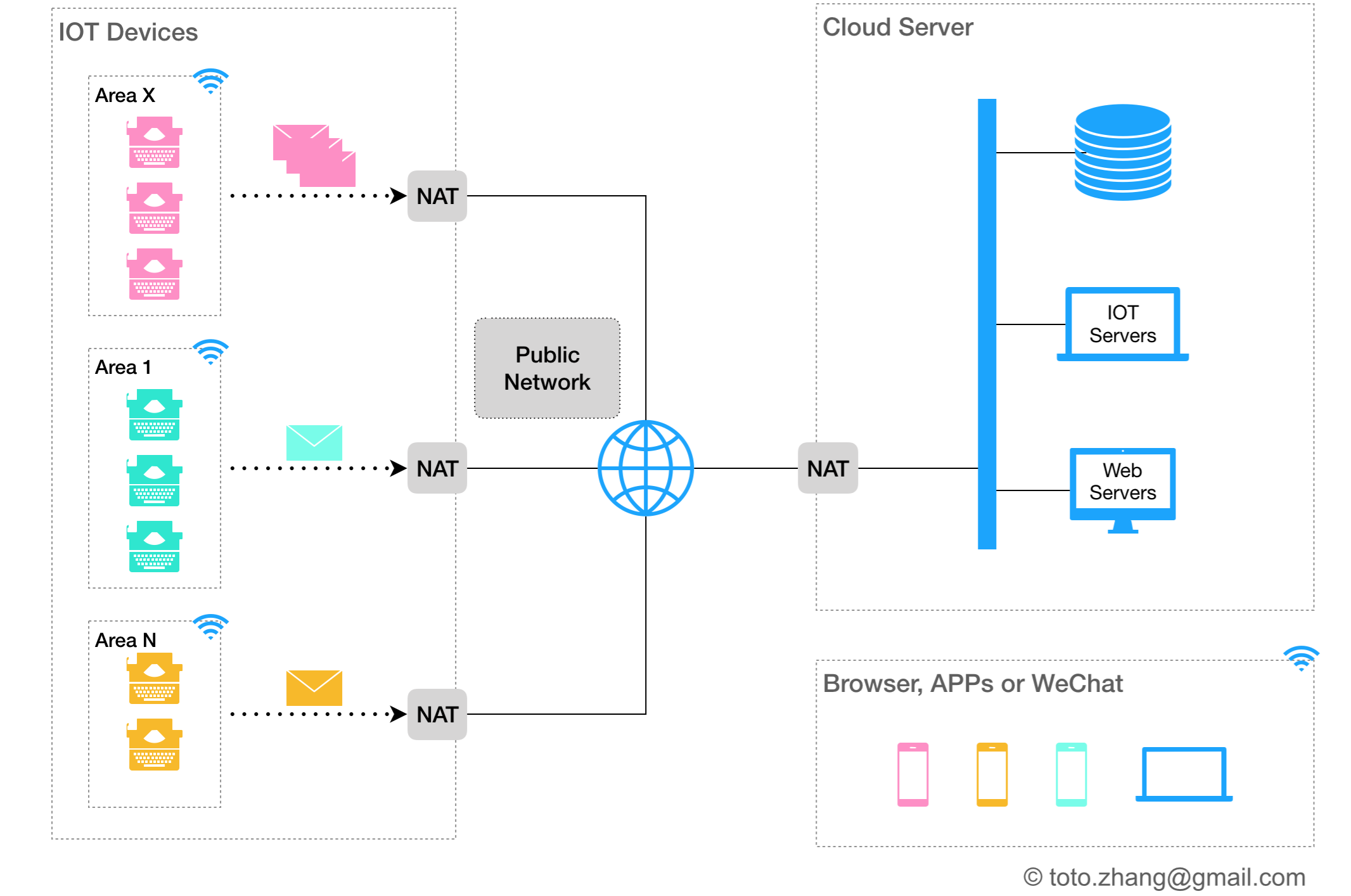
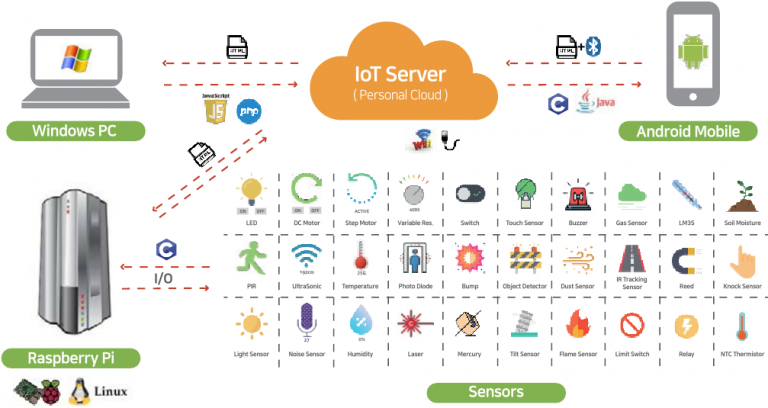
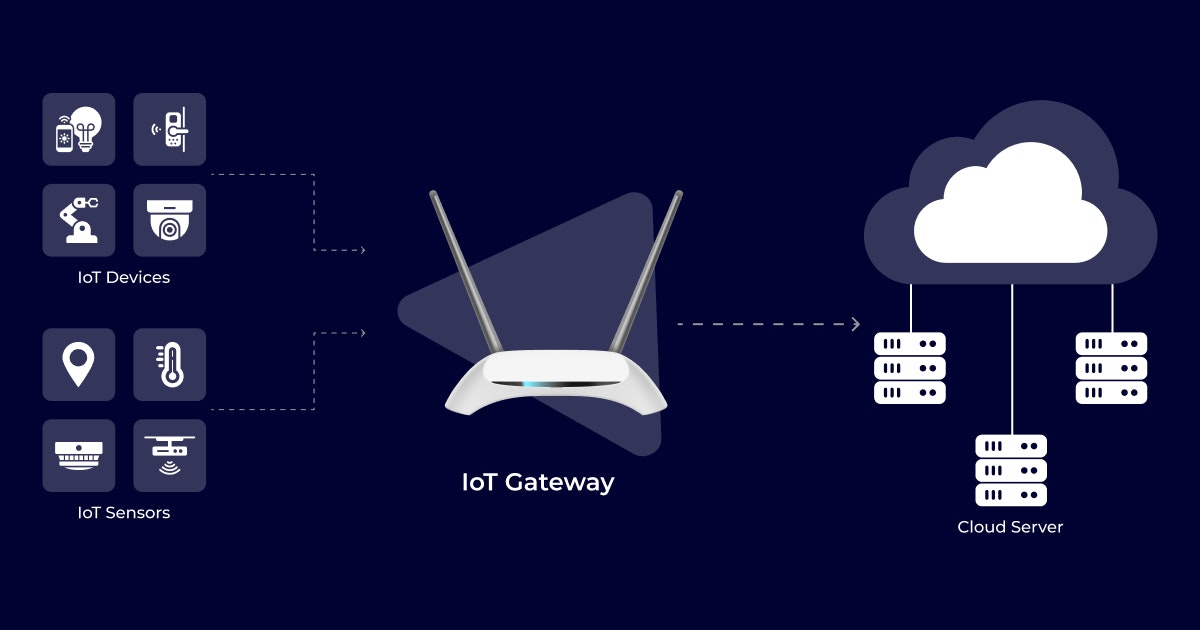
How to setup your own secure IoT cloud server: $1 a month IoT service manages 10,000 edge node - YouTube

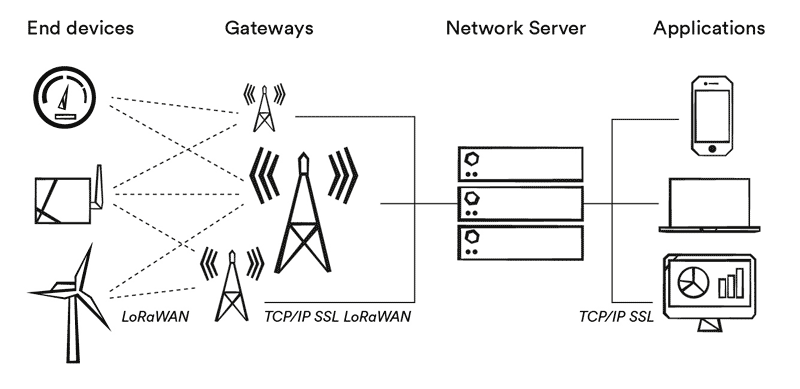
Over 100 million IoT devices and servers are vulnerable because of 20-year-old TCP/IP stacks | TechSpot
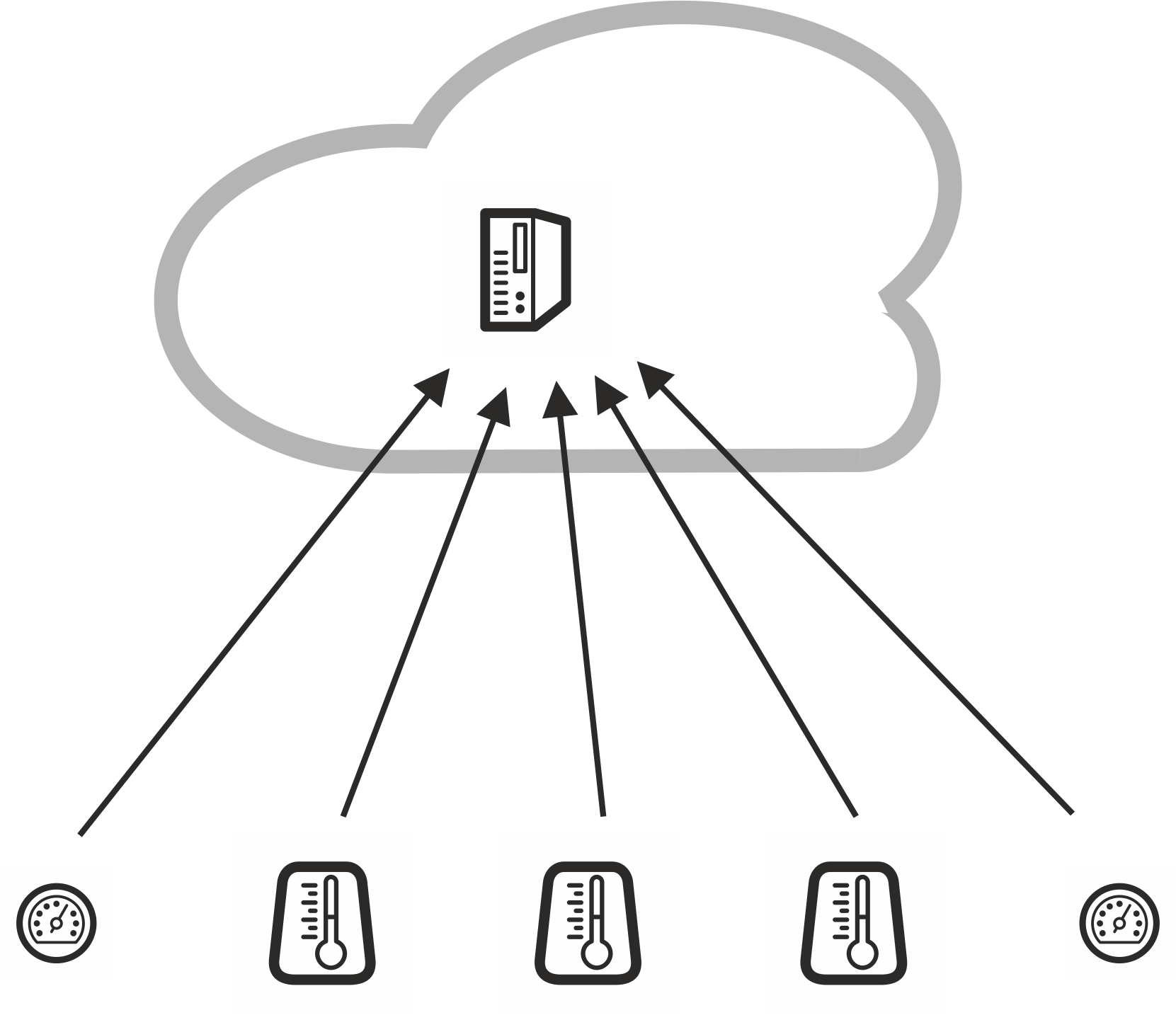
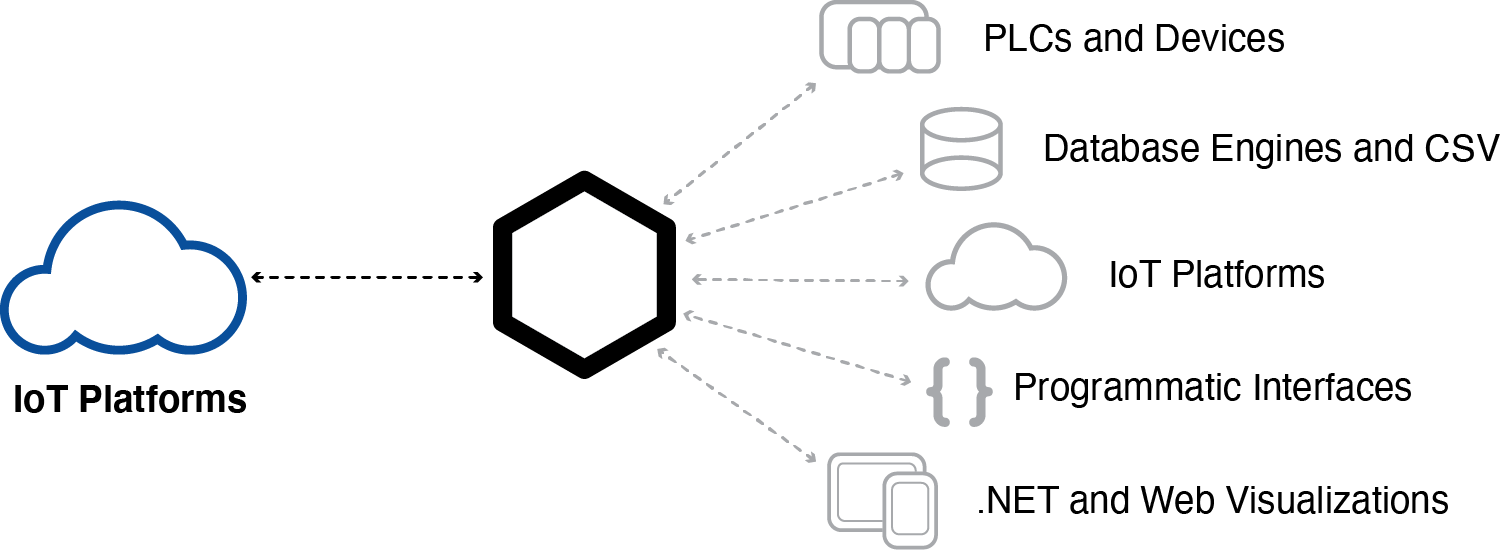
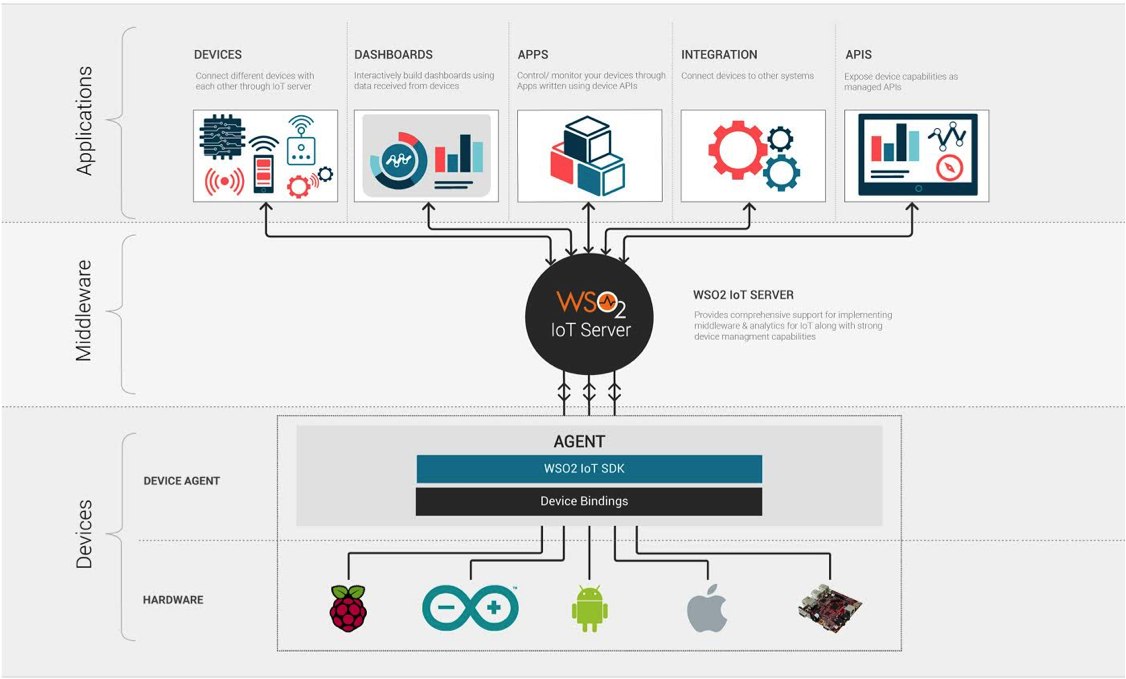
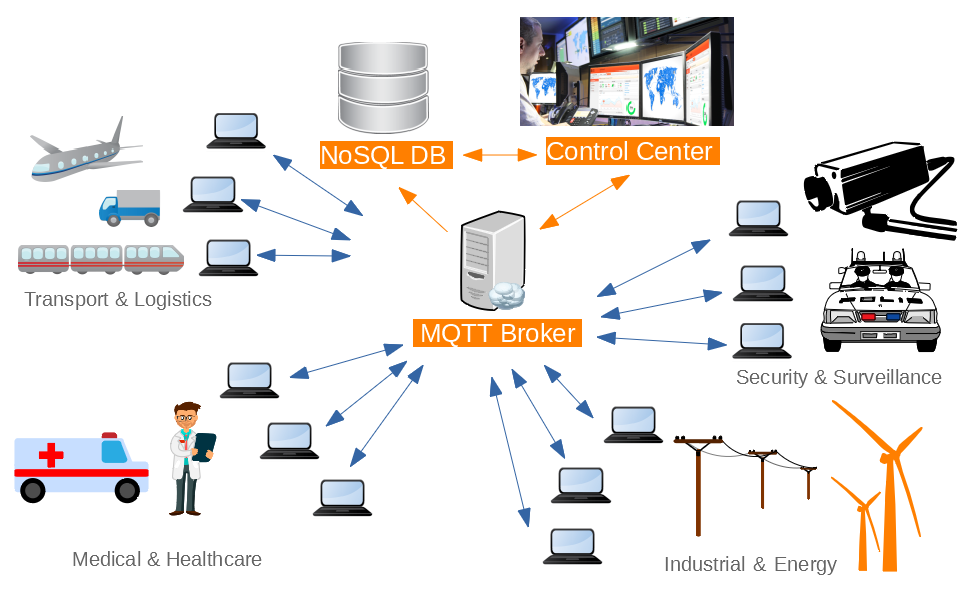
Fog computing for IoT applications consisting three layers: (i) Cloud... | Download Scientific Diagram