Association between the Infant and Child Feeding Index (ICFI) and nutritional status of 6- to 35-month-old children in rural western China | PLOS ONE

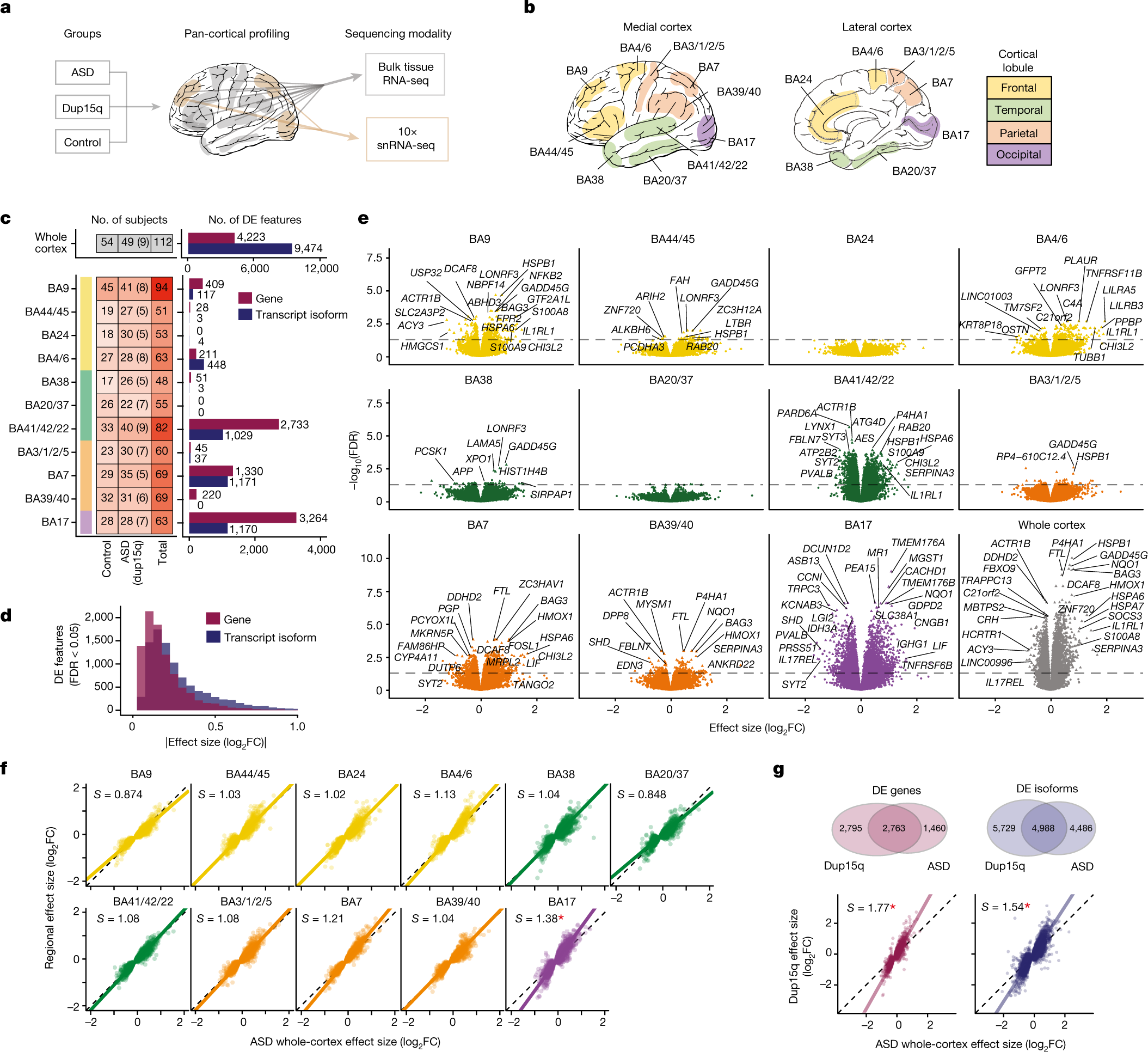
Autism-linked gene FoxP1 selectively regulates the cultural transmission of learned vocalizations | Science Advances

Autism spectrum disorder screening in Chinese-language preschools - Kathy Kar-man Shum, Rose Mui-fong Wong, Angel Hoe-chi Au, Terry Kit-fong Au, 2022
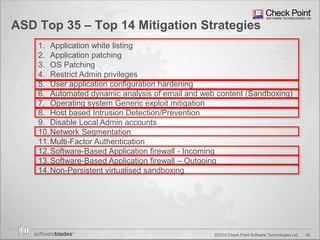
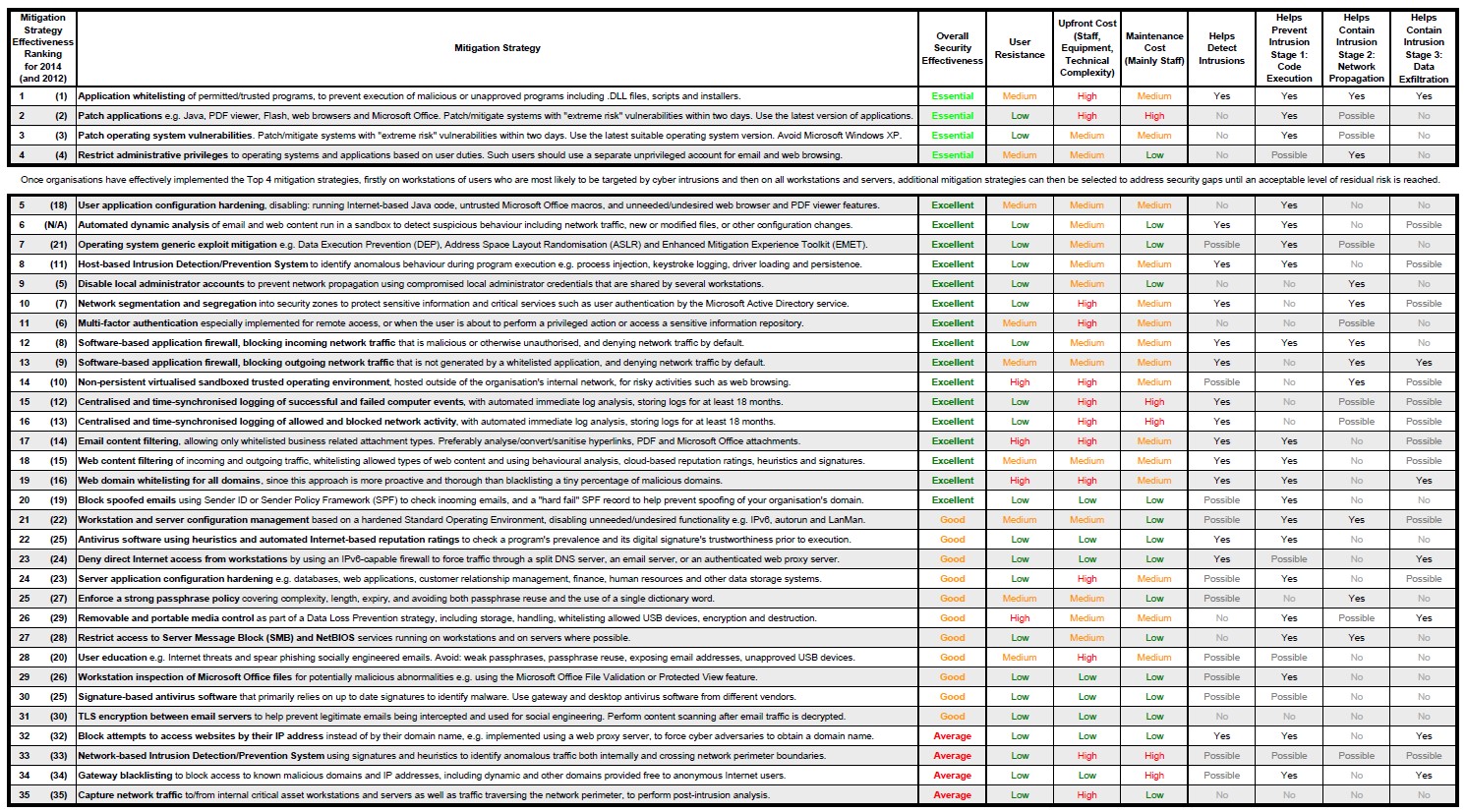
Chapter 12 Operating System Security Strategies The 2010 Australian Signals Directorate (ASD) lists the “Top 35 Mitigation Strategies” Over 85% of. - ppt download

Idiosyncratic Brain Activation Patterns Are Associated with Poor Social Comprehension in Autism | Journal of Neuroscience
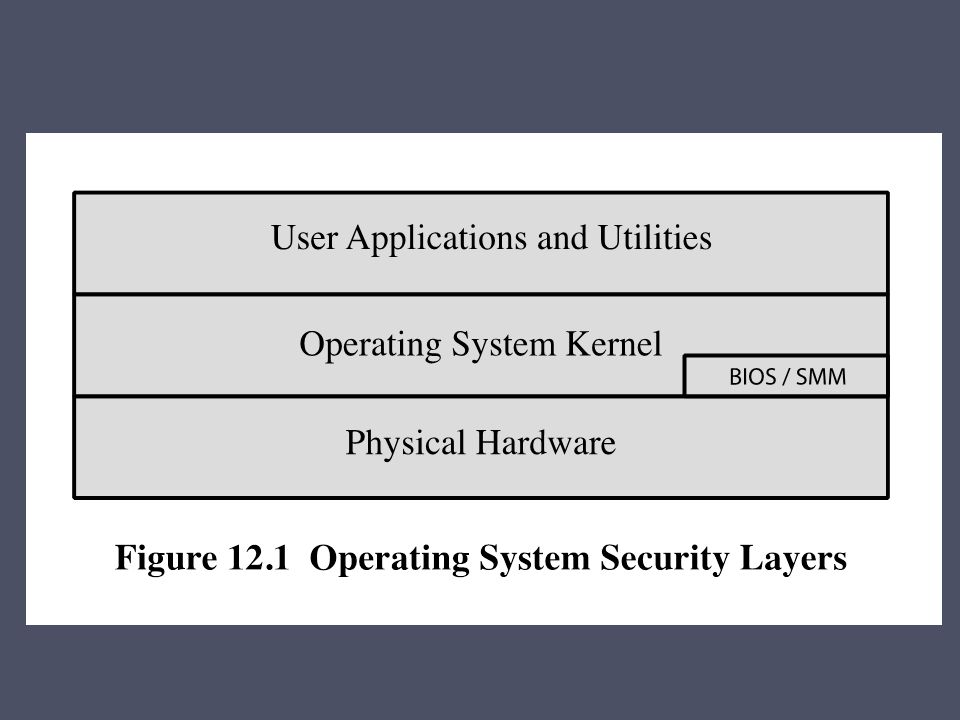
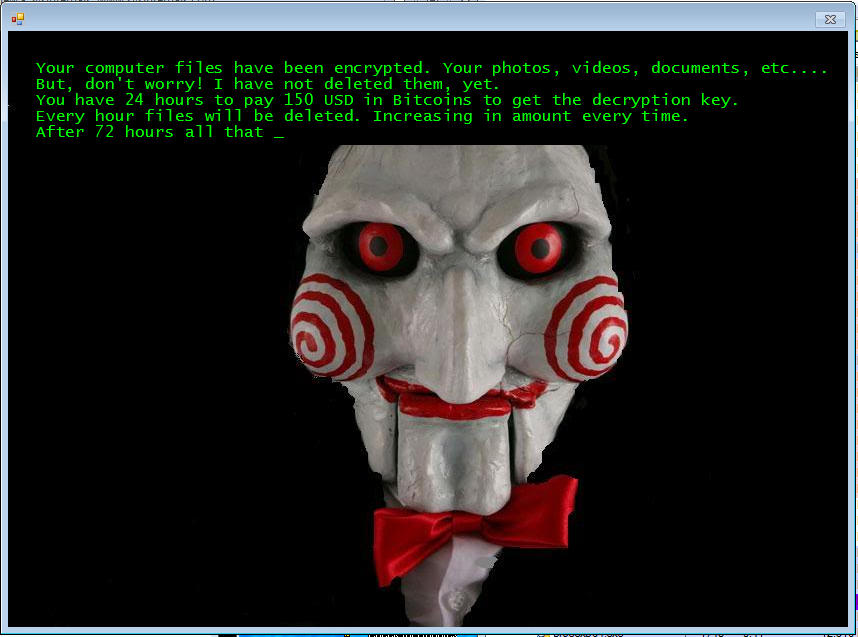
Chapter 12 Operating System Security Strategies The 2010 Australian Signals Directorate (ASD) lists the “Top 35 Mitigation Strategies” Over 85% of. - ppt download
The Military Cyber-Maturity Model: Preparing Modern Cyber- Enabled Military Forces for Future Conflicts

Mean scores on ASC-ASD subscales and overall scale for participants... | Download Scientific Diagram